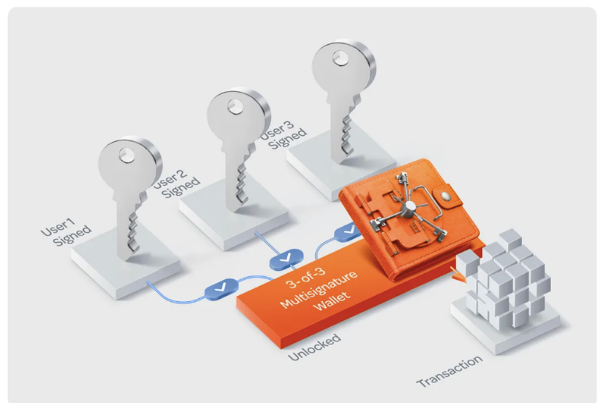
Multi-signature wallets distribute control across multiple keys, requiring M-of-N approvals to authorize a transaction. This design increases resilience and auditability but adds governance and deployment complexity. Key choices include participant selection, thresholds, and security practices, with attention to dispute resolution and rollback plans. The approach offers disaster recovery and governance benefits while presenting centralization risks and setup challenges. The balance between safeguards and operational burden invites careful consideration before implementation. The implications merit further examination.
What Is a Multi-Signature Wallet and Why It Matters
A multi-signature (multi-sig) wallet is a cryptographic scheme that requires multiple independent approvals, or signatures, to authorize a transaction, rather than a single private key. This construct distributes control, potentially increasing resilience. However, security risks persist through mismanagement and software flaws.
Adoption challenges include interoperability, user education, and key custody responsibilities, which must be weighed against enhanced control and accountability.
How Multi-Sig Works: Keys, M-of-N, and Dispute Resolution
How do multi-signature wallets impose control across participants while preserving security guarantees? Keys are distributed among signers, enabling M-of-N thresholds to authorize transactions. Dispute resolution protocols delineate failure modes and dispute handling, preserving integrity under contested actions. The design supports disaster recovery and onboarding incentives by outlining clear recovery paths and initial participation rewards, while avoiding centralized single points of failure.
Choosing a Multi-Sig Setup: Participants, Thresholds, and Security
Choosing a Multi-Signature setup requires careful selection of participants, an appropriate signing threshold, and robust security considerations. The arrangement should balance decentralization with operational practicality, ensuring diverse key management and clear authority. Thresholds determine fault tolerance and recovery paths. Consider network fees implications and potential recovery scenarios, evaluating risk, governance, and auditability to sustain autonomy without compromising protection or transparency.
Practical Guide to Deploying a Multi-Sig Wallet: Setup, Testing, and Gotchas
Deploying a multi-signature wallet involves a structured sequence of setup, rigorous testing, and awareness of common pitfalls to prevent operational risk.
The guide emphasizes reproducible deployment steps, secure key management, and environment isolation, with explicit security audits and rollback plans.
It highlights user onboarding, documentation, and role-based access to minimize error rates while preserving autonomy and transparent governance.
Frequently Asked Questions
What Are Common Misconfigurations to Avoid in Multi-Sig Setups?
Common misconfigurations include weak key storage and inadequate backups; misconfigured backups and key storage failures threaten recoverability. They emphasize practice: compartmentalized, redundant storage, verified key transfers, and immutable logging to reduce operational risk in decentralized control systems.
How Do You Recover Funds if a Key Is Lost?
If a key is lost, recovered access relies on redundancy and provenance: lost key recovery via backups, hardware shares, and recovery scripts; daily use restores hinge on defined thresholds, quorum policies, and secure multisig vault procedures.
Can a Multi-Sig Be Hacked Through Social Engineering?
Yes, a multi-sig can be compromised via social engineering, phishing attacks, insider threats, or misused key escrow; safeguards require strict authentication, separate operational security, and least-privilege access to mitigates risks while preserving user autonomy.
See also:AI in Collaboration Platforms
How Do Multi-Sig Wallets Handle Key Rotation?
Ironically, rotation occurs methodically: multi-sig systems rotate keys via defined schedules, separate signing keys, and revocation procedures. Key rotation minimizes risk, while security auditing validates changes, enforces constraints, and preserves autonomy for users seeking freedom within controls.
What Compliance or Regulatory Considerations Apply to Multi-Sig?
Regulatory considerations depend on jurisdiction, but generally involve compliance frameworks, license requirements, and ongoing regulatory reporting. Multi sig governance must align with risk controls, auditability, and fiduciary duties, ensuring transparent processes while preserving operational freedom within legal boundaries.
Conclusion
In the end, a multi-signature wallet is a compass with many needles. Each key is a star in a night sky, signaling trust only when several align. The threshold is the north, guiding direction but demanding consensus to move. When misalignment occurs, the coins drift like fog, unresolved and exposed. Properly configured, tested, and governed, it becomes a resilient vault; improperly managed, it mutters to itself, a chorus of quiet, unresolved alarms.